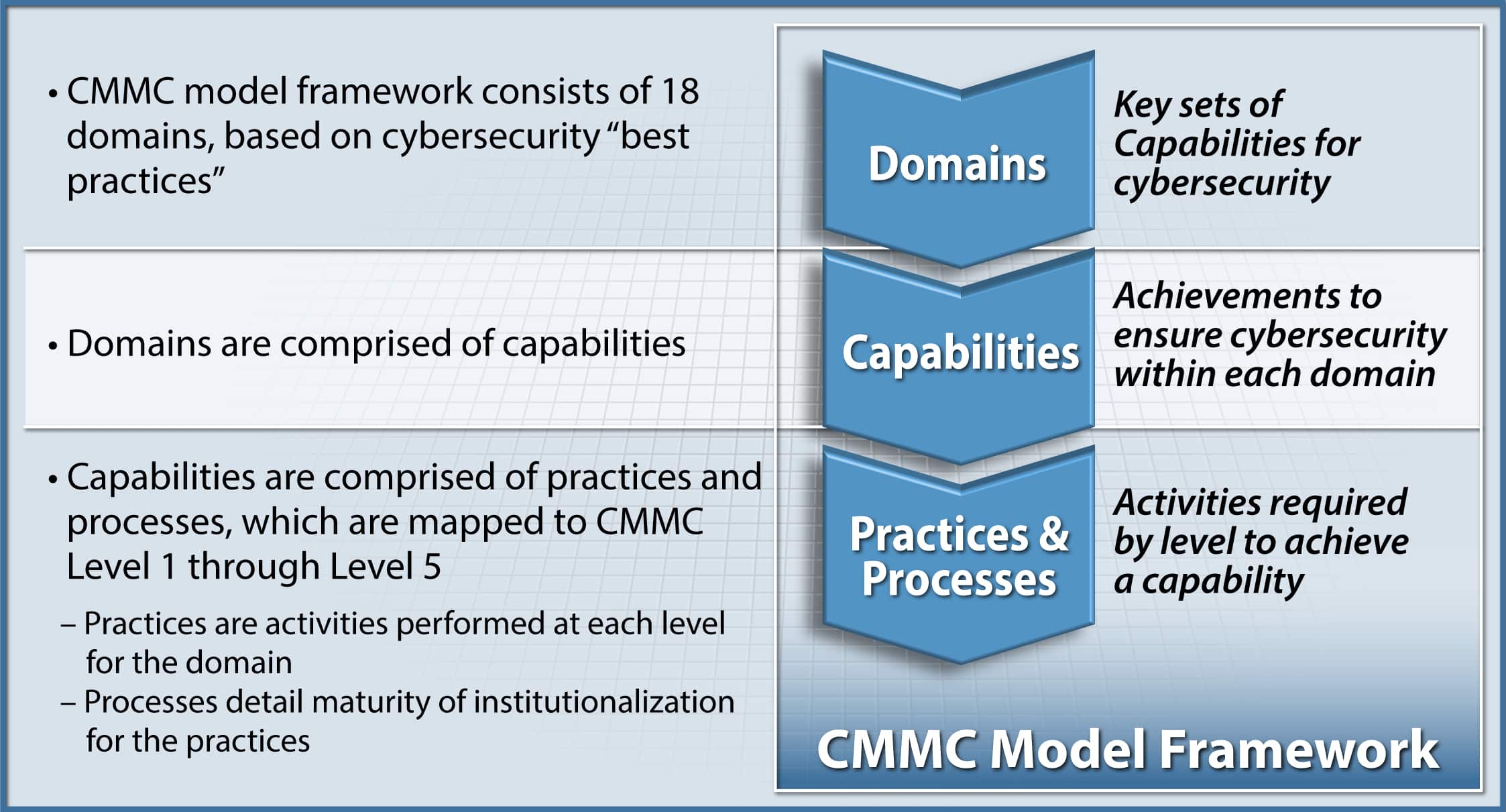
With the release of CMMC Version 1.0 of the Cybersecurity Maturity Model Certification on January 31st, 2020, the Department of Defense’s efforts to codify a comprehensive and robust cyber security standard and certification for defense contractors who process, store or transmit Controlled Unclassified Information (CUI) have reached completion. In no uncertain terms, this mandatory standard will directly impact your ability to bid on, and ultimately win, federal contracts.

Perhaps of more urgent note, actual NIST SP 800-171 audits, conducted by the Defense Contract Management Agency, or DCMA, began for Tier 1 contractors in January 2020 as well. By extension, the organizations in the supply chains of the various Tier 1 providers can expect more scrutiny in the near future and, as has already been the case, to potentially be dismissed by the Tier 1 provider they are associated with if they cannot demonstrate a meaningful commitment to achieving cyber compliance.
Additionally, on November 8th, 2019 it was also determined that defense contractors that receive Federal Contract Information, or FCI, will very likely be required to achieve a CMMC Level 1 or 2 classification regardless of whether they handle CUI. Translated, the DoD is now considering the possession of an RFP as a cyber vulnerability.
Unquestionably we find ourselves in a fluid situation as it relates to timelines and other variables impacting the DoD’s unyielding emphasis on cyber hygiene and compliance requirements. That said, the good news is that we now have a clear standard to apply and benchmarks to achieve.
The clear reality is that DoD proposals have an increasing focus on cyber awareness, with cyber security being considered a foundational, non-negotiable “pillar of consideration” alongside schedule, performance and cost. This makes compliance with the CMMC standard a business development issue as well, not just a tech issue as its been viewed by many in the past.
Contact us

